Red Team Assessment versus Penetration Testing
We often hear them reciprocally, but in fact, they’re 2 distinct things. So what is the difference between these 2 terms Red Team Assessment and Penetration Testing precisely? In this article, we’ll explain, with the goal to help you learn more about which one might be the best fit for your organization.
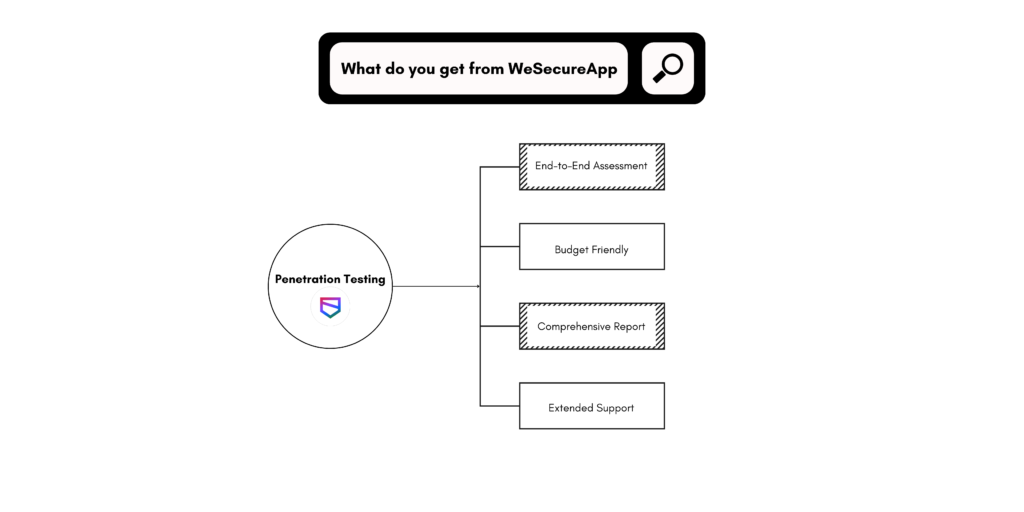
Penetration Testing
Generally, penetration testing is turned into one huge umbrella with all security considerations. Many people do not realize the differences between a Red Team Assessment, a Penetration Test, and a Vulnerability Assessment. Hence they call them all Penetration Testing. Nevertheless, this is a delusion. Though they have related components, each one is different and must be used in diverse contexts.
At the foundation, Penetration Testing identifies as many configuration issues and vulnerabilities as possible in a fixed duration of time and exploits those vulnerabilities to figure out the risk of the vulnerability. This does not basically mean illuminating new vulnerabilities; it’s more of looking for well-known, unpatched vulnerabilities. Similar to vulnerability assessments, penetration testing is intended to find vulnerabilities and evaluate them to make certain they are not false positives. nevertheless, Penetration testing digs further, as the tester tries to exploit the vulnerability.
How is Penetration Testing performed?
This can be done in various ways, and even when the vulnerability is exploited a good tester will not stop. They will carry on to search and exploit new vulnerabilities, processing attacks together to attain their goal. This goal keeps changing, as every organization is unique, but generally, it comprises PHI (Protected Health Information), PII(Personally Identifiable Information), and trade secrets. Sometimes it may need Domain Administrator access.
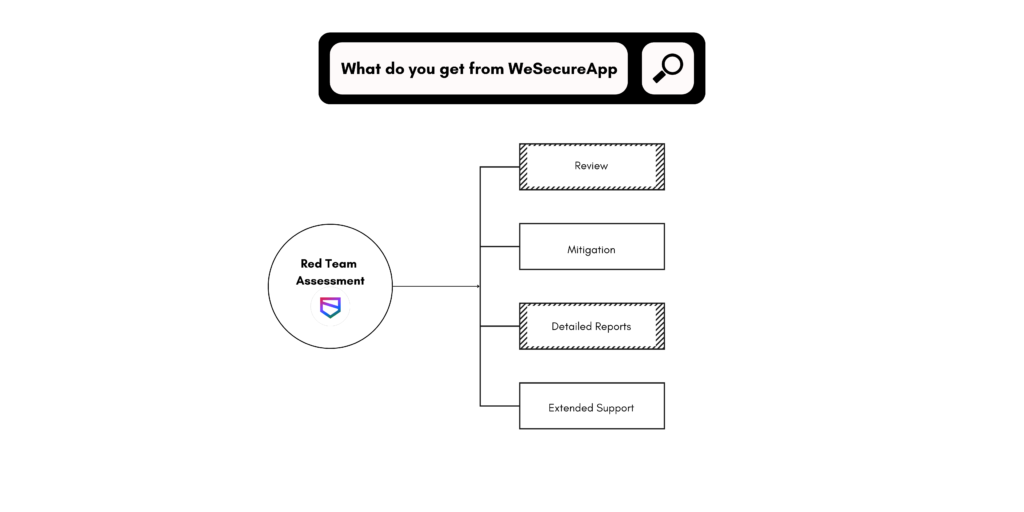
Red Teaming
In comparison to penetration testing, Red Teaming is focused on target objectives. Instead of hunting for vulnerabilities, the red team puts in efforts to check how the security teams of an organization react to different threats. The Red Team will always concentrate on the objectives, in the hunt to achieve access to receptive data in furtiveness, preventing detection.
Usually, a Red Team Assessment will design detailed objectives and the progression will involve a lot more people than a typical penetration test. In expending more time on investigation and wanting more resources, the Red Team Assessment may result in a more deep comprehension of the level of risk that known security vulnerabilities might cause to the organization.
Why Red Team Assessment
Attackers use numerous techniques to breach an organization. Being tough to modern attack tactics is the only optimal solution for this. You need to spot security loopholes that are consumed by APT groups and repair them to avoid security breaches.
Red Team Assessment can help you in the following way,
- Put your perimeter security to test with a simulation of a real-world attack on your organization.
- See how your incident response team responds to real-world threats through Stress-tests.
- Authenticate your security controls for crucial infrastructure.
- Get immune to the real-world attacker’s tactics.
- Ensure your threat prevention program is bullet-proof.
- Obtain a virtual view of your organization’s public-facing assets and construct defenses around them.
Duration
The duration of the Red Team Assessment is usually longer than Penetration Testing. Red Team Assessment occupies multiple people and typically lasts for more than 3-4 weeks, whereas a Pen Test habitually takes place over 1-2 weeks.
Goals and Methods
Instead of hunting for multiple vulnerabilities, Red Team Assessment looks for vulnerabilities that would help them to achieve their goals. Normally the goals resemble a pen test. A Red Team Assessment method involves Social Engineering (both Physical and Electronic) Wireless, External, and more.
Which to Prefer?
You certainly wouldn’t hire ninjas to find every buried treasure in a specific piece of land. Similarly, you wouldn’t want to send noisy pirates to perform stealth missions.
That’s exactly the point we wanted to make. When you’re considering which one to choose between red teaming and pen-testing, it all depends on what you’re looking for.
Our advice is to use pen testing if your organization’s security is in the early stages. If your company relies on mature security programs, we would suggest trusting a red team. Whichever you choose, one thing is certain: You’ll be on your way to joining the 58% of business owners who have increased their digital security budget following the arrival of the pandemic, according to a survey conducted by Microsoft.
Generally, Pen-Testers and Red Teams are the same people who use divergent procedures and methods for different assessments. Superlatively, one is not essentially better than the other. It’s just that each is supportive in particular scenarios.
For example, a Pen-Test is not prudent to judge how good your incident response is and a Red team assessment is not prudent to discover vulnerabilities. It all depends on the circumstances and scenarios that would help us opt for the better one.
Conclusion:
Red Team Assessment services help you to identify and address attacks. Stay ahead of the rapidly evolving threat landscape and keep your data protected without having to spend a fortune. Pentesting may be performed by remote teams, through scheduled assessments, analysis, and reporting. Technology firms also regularly work with remote testers, to receive new insights into their system architecture. While not all red team and purple team engagements can be done remotely, a large portion of pentesting may be performed off-site.
Gone are those days when attackers only used unpatched vulnerabilities to breach an organization. Information Security has come a long way and now organizations have dedicated security teams to prevent security breaches.
Let WeSecureApp organize all your cyber-security challenges. Get aggressive security quotes by just clicking below. We look forward to hearing from you.