The Hidden Threat to Sensitive Data and Security
Sensitive data and security are critical concerns in today’s digital age. With the rise of cybercrime and the increasing use of digital devices, it is essential to take precautions to protect sensitive information from unauthorized access, theft, or misuse. One of the biggest threats to sensitive data and security is the hidden threat. Hidden threats refer to vulnerabilities and risks that are not immediately visible or apparent.
The hidden threat to sensitive data and security can come from a variety of sources. Here are a few examples:
- Insider Threats: Employees, contractors, or other insiders with access to sensitive data can pose a significant threat to data security. They may intentionally or unintentionally leak sensitive information, steal data, or compromise systems. Insider threats can be difficult to detect because the individuals involved have legitimate access to the data and systems they are targeting.
- Phishing and Social Engineering Attacks: Cybercriminals often use phishing and social engineering attacks to trick people into revealing sensitive information. These attacks can take many forms, including fake emails, phone calls, or social media messages that appear to be from trusted sources. Phishing and social engineering attacks can be difficult to spot, and they can be very effective at tricking people into divulging sensitive data.
- Malware and Ransomware: Malware and ransomware are types of malicious software that can be used to steal sensitive data or disrupt systems. Malware can be introduced into a system through infected emails, downloads, or other methods. Ransomware can be particularly damaging because it can lock users out of their systems and demand payment in exchange for restoring access.
- Third-Party Risks: Organizations often rely on third-party vendors to handle sensitive data and perform critical functions. However, third-party vendors can introduce additional risk to an organization’s data security. Vendors may have weaker security controls or may be vulnerable to attack, which could put sensitive data at risk.
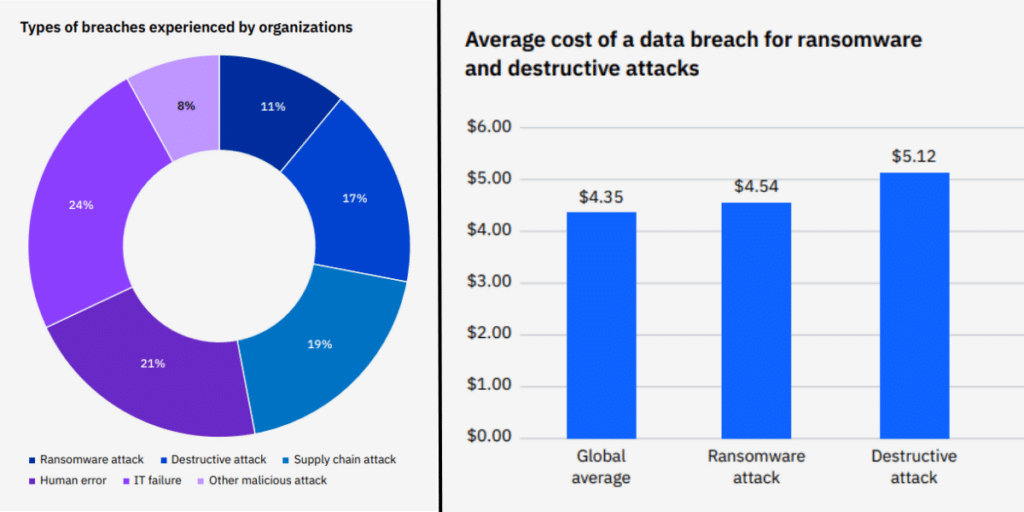
Source: IBM
To mitigate these threats, organizations should implement strong security measures, such as multi-factor authentication, data encryption, and regular security training for employees. It is also important to conduct regular risk assessments and monitor systems for suspicious activity.
The Financial sector continues to be victimized by financially motivated organized crime, often via the actions of Social (Phishing), Hacking (Use of stolen credentials) and Malware (Ransomware). Finally, Miscellaneous Errors, often in the form of Misdelivery, is still very common as it has been for the past three years in a row. 2,527 incidents, 690 with confirmed data disclosure. Basic Web Application Attacks, System Intrusion, and Miscellaneous Errors represent 79% of breaches.
Here are some statistics related to the hidden threat to sensitive data and security:
- Insider threats account for about 39% of all data breaches. (Source: Verizon’s 2022 Data Breach Investigations Report)
- Phishing attacks accounted for 36% of all data breaches in 2022. (Source: Verizon’s 2022 Data Breach Investigations Report)
- Ransomware attacks increased by 62% in 2022, with the average ransom demand increasing by 43%. (Source: SonicWall 2022 Cyber Threat Report)
- Third-party data breaches have increased by 60% since 2022. (Source: Ponemon Institute’s 2022 Cost of a Data Breach Report)
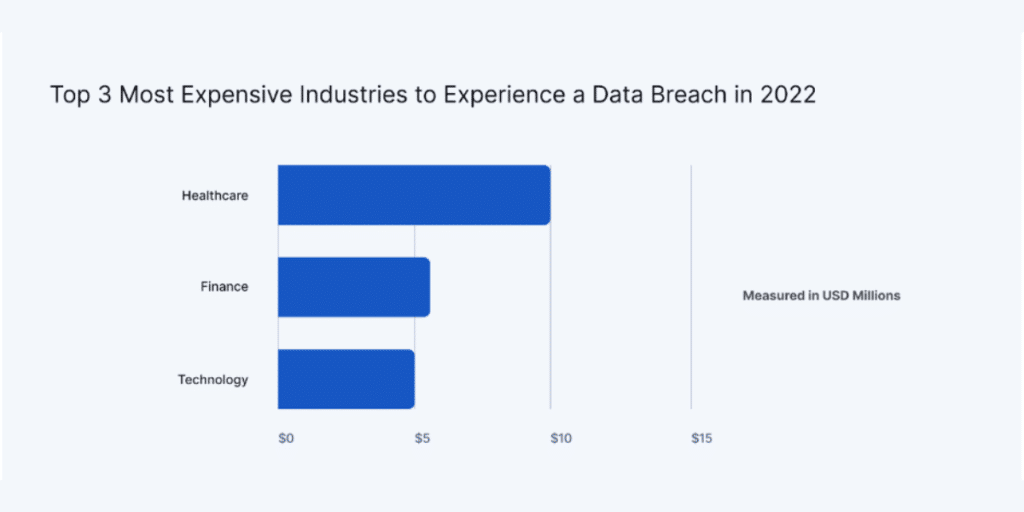
- The average cost of a data breach in 2022 was $4.35 million. (Source: IBM Security’s 2022 Cost of a Data Breach Report)
These statistics highlight the importance of taking proactive steps to protect sensitive data and systems. Organizations must prioritize security measures such as employee training, multi-factor authentication, and regular risk assessments to mitigate the risks of data breaches and cyber attacks.
Conclusion:
The hidden threat to sensitive data and security is a serious and ongoing concern for organizations of all sizes and industries. Organizations must take a proactive approach to mitigate these risks by implementing strong security measures and conducting regular risk assessments. This includes employee training, multi-factor authentication, data encryption, and monitoring systems for suspicious activity.
The consequences of a data breach or cyber attack can be severe, resulting in financial losses, reputational damage, and legal repercussions. By prioritizing data security and taking proactive measures to protect sensitive information, organizations can reduce the likelihood of a breach and safeguard their data and systems.
Recommended Reading:
Ransomware as a Service – The Trending Business Model for Attacks
Browser-in-the Browser (BITB) – A New Born Phishing Methodology