Do you have an Incident Response Plan? Here is a Checklist
The digital world is growing every moment of the day, from buying safety pins to plane, doing transactions to socializing with friends, everything is digitalized. This digital world collects all data like name, ethnicity, card details, etc., and protecting that is of utmost importance. As an organization, if you are collecting such data, the question you must ask yourself is, “Whether you’re prepared to tackle and safeguard your IT infrastructure from any security incident?” If the answer to the question is “NO” then you need effective Incident Management.
As per the research, we have to prepare for “what to do in the attacked situation” instead of “what to do if we are attacked”? An incident management plan is your best shield to defend your organization from safeguarding the after-effects of a data breach. The time required to plan and define your action for security incidents–whatever they may be–is far off before it occurs.
What is an Incident Management Plan?

source : https://www.varonis.com/blog/incident-response-plan/
An Incident Response Plan is a set of actions to be performed when an Incident occurs. These actions help us to protect our data in case a company’s IT assets are attacked. The plan guides our actions to detect, respond and recover from security incidents.
There are industry-specific standards that provide guidelines for incident response frameworks of organizations, these standards are provided by institutions like NIST and SANS that avails general guidelines on how to respond to an active incident. Your organization’s Incident Management Plan, however, should be much more relevant—with an action plan like who should do what and when during an Incident.
An Incident Response Plan should have 6 steps:
- Plan
- Detect
- Quarantine
- Remediate
- Returning back to Normal
- Review
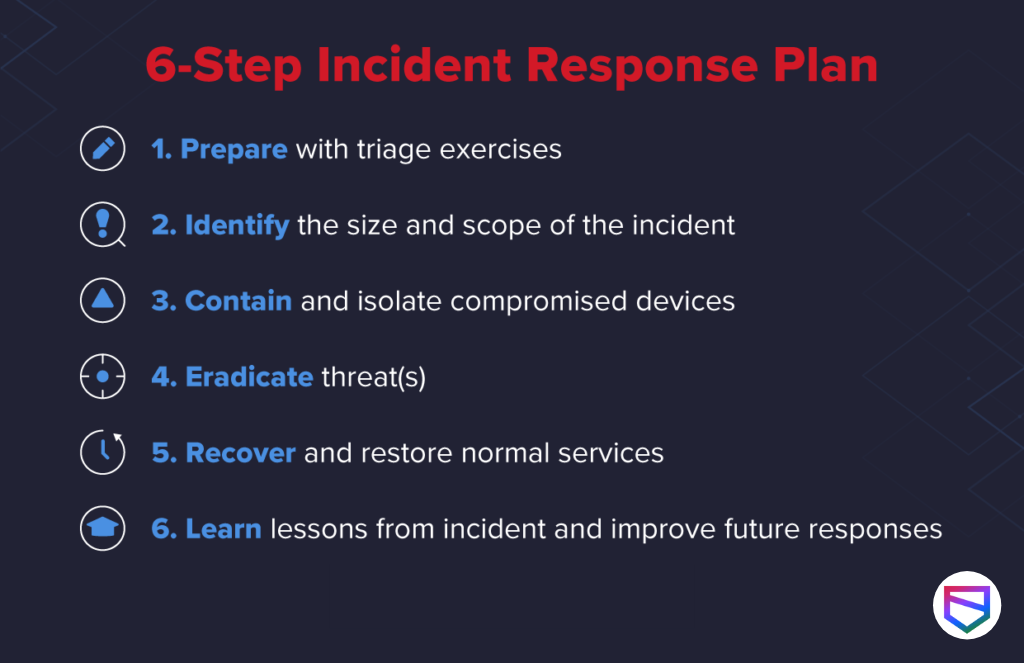
- Plan – Incident Management Plan should be well-drafted and effective to deal with any type of new-age security incident. The plan should be communicated to all the employees who are part of it, and well aware of their role. As the employees working to safeguard the organization is the strongest wall to be breached, all employees must be trained in form of a security drill.
- Detect – Implementation of proper SIEM (Security Incident Management) Tool, that has the capacity to detect any type of bug, malware, or force breach, and it should alarm to a responsible person if it detects any threat to companies infrastructure. And, the person should have all rights to stop or eradicate the same.
- Quarantine – All evidence with regards to breach (how and where it started) must be retained for that the affected system should be pulled out of the network, so that it doesn’t harm other IT assets and must be quarantined to review logs of the same. It’s highly advisable to have your system backed up at regular intervals to help restore business operations in a timely fashion. This way, any affected data isn’t lost forever.
- Remediate – Once the assets are quarantined, you must identify the root cause of the security breach, and all malware should be eradicated. Identify the source and hardened and patch all your IT assets to prevent such breaches in the future.
- Back to Normal – Once all the precautionary measures are taken, review the affected system for no traces of malware. Once we are sure that the affected system is clean, introduce it back to business and keep an eye over the asset, that it doesn’t go rogue again because of any traces from the past breaches.
- Review – Once the examination process is complete, organize a review meeting with Incident Response Team members and review the lessons learned from the security incident. During this stage, you will analyze and record everything about the breach. You should review the process to see what went well in your response plan, and where did we lack to support or realized loopholes. Lessons learned from mock and real-time events always help to strengthen your systems and perform better against future attacks.
Conclusion
Having an efficient Incident Management Plan and testing it regularly prepares you for actual Incident-related actions. An Effective Incident Management Plan leads you with examples of “How to deal with incidents in a most effective way and returning back to normal business operation in the least possible time,” and a bad plan makes you an example of the repercussions of a security breach. For having highly effective Incident Management Tools & Systems for your organization, you need an expert to develop each stage of Incident Management. WeSecureApp is the best door to knock, to get all your queries answered and infrastructure-related tools set up that gives real-time solutions to all security incident coming your way.
Get your Incident Management Plan reviewed and defined to tackle new-age security incidents in the most efficient way with WeSecureApp – – Talk to Our Delivery Head