Healthcare Cybersecurity: Ensure the security of private health data
Healthcare data is some of the most sensitive information out there, and it’s essential to keep it secure. After all, this data can include things like Social Security numbers, addresses, and health information.
With around 1200 cyber attacks every day, equating to 39 seconds per minute, it’s no wonder that healthcare organizations are a prime target for hackers. 60 percent of large healthcare organizations have reported being hacked in the past year.
All the healthcare service providers, hospitals, clinics, and doctors have to balance protecting patient privacy and safeguarding PHI (protected health information) against the potential harm of a large-scale data breach. They should meet all the strict regulatory requirements set forth by the HIPAA (Health Insurance Portability and Accountability Act)
However, many healthcare cybersecurity professionals will attest that achieving and maintaining HIPAA compliance is an ongoing challenge. But, nothing is impossible if you put your mind to it.
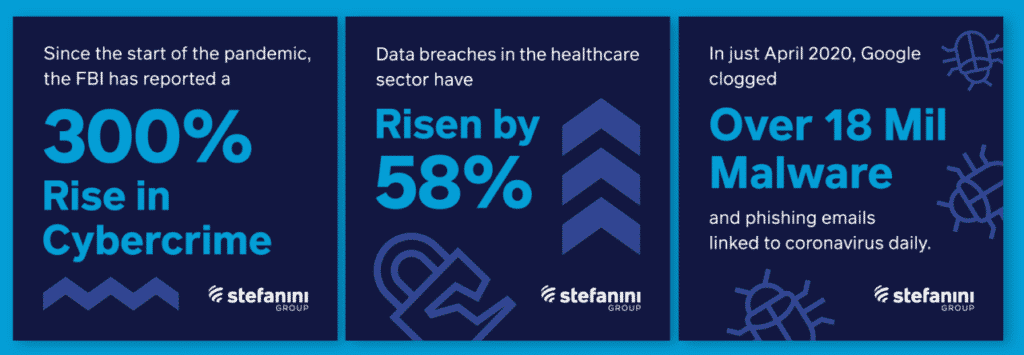
Source: Stefanini Group
Many compliance practices exist today; even electronic health records (EHR) systems have security features to help prevent unauthorized access.
Even EHR vendors and other third-party service providers cannot be solely relied upon to ensure data security as they have their own procedural and technical vulnerabilities.
So, all these alone cannot provide foolproof security to the organization. There are always new threats and vulnerabilities emerging, so the security team has to be on their toes.
Luckily, there are some practices that healthcare organizations of all sizes can implement to help protect against data breaches, malware, and other cybersecurity threats. Read on to find out more.
Top Healthcare Cybersecurity Tips
1. Establish a Strong Cybersecurity Framework
Developing a comprehensive healthcare cybersecurity framework should be the first step for any healthcare organization looking to strengthen its cyber defenses.
There are many different frameworks, but one of the most popular is the NIST Cybersecurity Framework. This framework guides managing and protecting your organization’s information and systems.
It’s essential to tailor the framework to your specific needs, as no two organizations are the same. But, the NIST Cybersecurity Framework can be a great starting point.
Pro Tips
-Organizations should develop a risk management program and identify which systems pose the highest risk.
-They should also implement security controls to mitigate those risks.
-Regularly test and monitor your systems to ensure they are still secure.
2. Use Strong Passwords and Authentication Methods
One of the easiest ways to improve your organization’s healthcare cybersecurity posture is by enforcing strong passwords and authentication methods.
This includes using unique passwords for each account, changing them regularly, and using a mix of letters, numbers, and symbols.
It’s also important to use two-factor authentication whenever possible. This process requires two forms of identification, such as a password and a code sent to your phone, to log in.
All this may seem like a lot of work, but it’s worth it to help protect your data.
Pro Tips
-You can use a password manager to help keep track of all your passwords.
-Two-factor authentication is available on many online services and mobile apps.
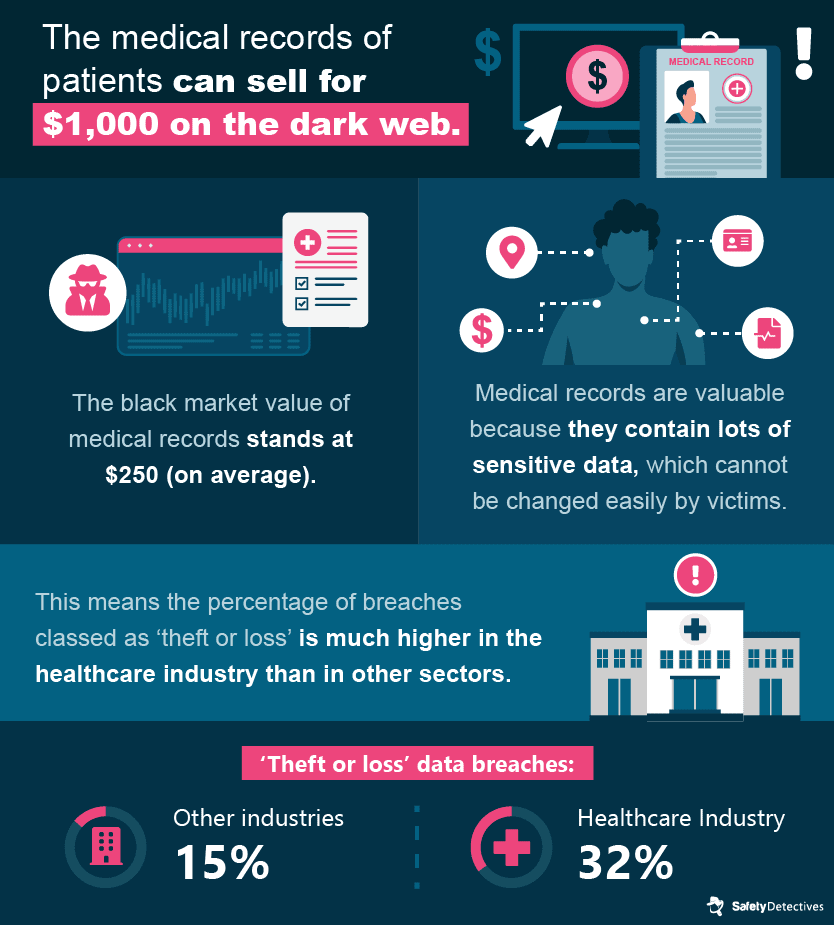
Source: SafetyDetectives
3. Educate Healthcare Staff on Cybersecurity Threats
It’s not enough to have strong healthcare cybersecurity measures in place; you also need to educate your healthcare employees on the dangers of cyber threats.
Many data breaches occur due to malicious insiders or employees who click on phishing links.
That’s why it’s essential to train your employees to identify and avoid such threats. You can also create policies and procedures that they must follow to protect the organization’s data.
Pro Tips
-Make sure your employees know the most common types of cyber threats.
-Teach them how to spot phishing emails and other malicious content.
-Create policies and procedures that they must follow to protect the organization’s data.
4. Use Secure Communication Methods
Encrypting your data is one of the best ways to protect it from cyber threats.
The data is converted into an unreadable format that authorized users can only decrypt.
There are many different encryption methods, but one of the most popular is HTTPS. It is a secure protocol that helps protect data as it’s being transmitted between devices.
Pro Tips
-Make sure all your organization’s data is encrypted.
-Use HTTPS whenever possible to help protect data in transit.
-Monitor your systems for any signs of encryption being breached.
5. Implement a Cyber Incident Response Plan
No matter how strong your healthcare cybersecurity measures are, there’s always a chance a cyberattack could hit you.
That’s why it’s essential to have a plan in place to respond to such an incident. This plan should include steps for containing the breach, investigating the cause, and restoring any lost data.
It’s also essential to practice this plan regularly to prepare if an incident does occur.
Pro Tips
-Include steps for containing the breach, investigating the cause, and restoring any lost data.
-Regularly practice this plan so that you’re prepared if an incident does occur.
6. Conduct Regular Cybersecurity Audits
It’s not enough to just have strong cybersecurity measures in place; you also need to check that they’re working as intended regularly.
This is known as a cybersecurity audit. There are many different types of audits, but they all involve inspecting your systems and procedures to ensure effectiveness.
Cybersecurity audits are essential because they can help identify any vulnerabilities in your system.
Pro Tips
-Conduct regular healthcare cybersecurity audits to ensure that your systems are effective.
-Identify any vulnerabilities that may exist in your system.
-Take steps to fix any vulnerabilities that are found.
7. Restrict Access to Sensitive Data
One of the best ways to protect your data is to restrict its access. It means that only authorized users can view and modify the data.
There are many different ways to restrict access, but one of the most common is user authentication. This involves verifying the identity of each user before they are allowed to access the data.
The best you can do is protect your data and make sure that it is only accessible by authorized users. So that in the event of a breach, the damage is minimized.
Pro Tips
-Restrict access to sensitive data through user authentication.
-Only allow authorized users to access the data.
-Verify the identity of each user before they are allowed to access the data.
-In the event of a breach, take steps to minimize the damage.
8. Utilizing Off-Site Data Backup
Another important step in securing your data is to ensure that you have a good backup plan. This means that you should regularly backup your data and store it off-site.
Data backup strategies can be complex, but there are a few things that you should keep in mind. First, you need to determine how often you need to backup your data. This will depend on how often your data changes and how critical it is.
Next, you need to decide where to store your backups. You should consider keeping them in a secure location such as a safe deposit box or an off-site data center.
Finally, you need to ensure that your backup plan is easy to use and reliable.
Pro Tips
-Make sure that you have a good backup plan in place.
-Store your backups in a secure location such as a safe deposit box or an off-site data center.
-Make sure that your backup plan is easy to use and reliable.
Conclusion
Healthcare data is a valuable asset, and it is essential to take steps to protect it. There are many different steps that you can take to secure your data, but the most important thing is to have a comprehensive security strategy in place.
Make sure that you review your healthcare cybersecurity strategy regularly and take steps to keep it up-to-date. And finally, make sure that your employees are aware of the importance of security and follow the security procedures you have in place.
PHI is very sensitive data. Let’s be ahead of hackers in securing it – Contact Us
Further Readings:
Stay HIPAA Compliant in this Work from Home Scenario
HIPAA: A US Federal law to protect health information
The Penetration Testing Guide for Compliance and Audits