Secure Code Review – A New Pace in Cybersecurity
Secure code review is a process performed manually as well as automatically that identifies security blemishes in an application’s source code. The ultimate aim of this review is to point out any existing security imperfections or open area weaknesses. Application’s Code review targets for logical errors, reviews specification implementation, and checks format guidelines, among other activities.
There are 2 ways to perform Code review.
Manual Review – An expert is hired for reviewing code line by line, to find the basic known scripting errors. Manual reviews help to understand the context of coding. Automatic Reviews are faster, but they don’t understand the intentions behind code and business logic. Manual reviews are pretty specific to business purposes and more strategic.
Automatic reviews – A code is passed through scripting software, to identify the known vulnerabilities through a predefined set of rules. This review is faster than manual review, but there is an amiss of logical intentions of the developer.
History of Code Review
Initially, the Code review was a lengthy and time-consuming process, where developers used to write long codes and it used to take days to review the code line by line. But due to automated review and Agile methodologies, the process of review has been very fast and constructive also. Drafting small codes, quick review and integrating them through scripting tools, make the count of developers intentions and strategies, quick correction in the initial stage of drafting codes, and resolution on pretty early stage.
Focal Point of Code Review
Cross-Site Scripting – The attackers try to embed malicious scripts in such a format that the user feels that it is legitimate by the use of cookies. This involves a compromised user with browser scripting.
Memory Flaw – The issues like Spectre or Meltdown are caused due to irregular and risky drafts of codes that lead to compromising the data stored in memory.
SQL Injection – The injection is a vulnerability that allows an application to accept the rogue commands, which are stored in a database and make applications more vulnerable.
Data Risk – Due to errors in coding a bad actor can access sensitive information likes PCI Data, PHI data, and PII data.
Why is it important to perform a secure code review?
Secure code review is a vital process deployed by some of the most successful development teams. It can help for following
- Decrease the count of final stage errors in the SDLC process.
- Reducing the amount of time the coders spend to fix last-stage defects, thereby increasing productivity.
- Shrink the number of code bugs and security exposure going into production.
- Improve deliverable effectiveness across coding and increase durability.
- Improve integration, knowledge transfers, and developer efficiency, with the lessons learned. This can help coders/ developers be informed while future code development.
- Increase in deliverables by making SOP process faster and more secure in nature, and being efficient while being effective
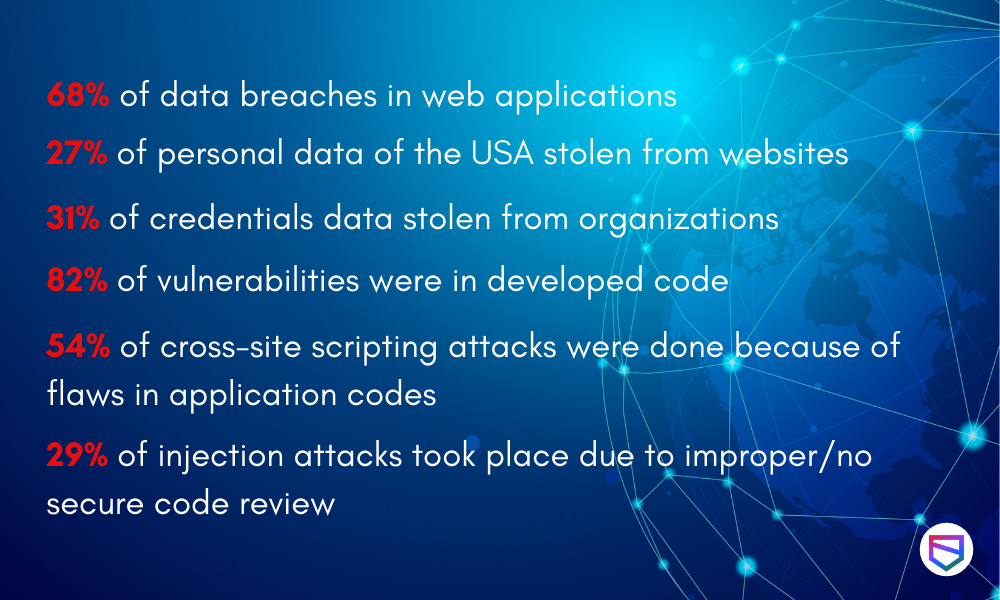
Some facts of attacks Due to Lack of Secure Code Review in 2019-2020
WeSecureApp – Bringing a new pace in cybersecurity
Code Review is one of the most important activities with regards to securing applications, It should be performed in a perfect blend of Automatic and Manual reviews, as some errors identified by automatic review could be falsely positive in manual review.
Our Methodology for Secure Code Review
Our secure code review methodology adheres to recognized and well-respected industry frameworks, including Open Web Application Security Project (OWASP), NIST, etc. This secure source code review services is a combination of human effort and technology support, which consists of going through the codebase and locating constructs that lead to vulnerabilities. We offer “baking in” security from the start of the development process, rather than trying to “brush it on” at the end. This helps you create secure applications that can withstand attacks.
Assess – Getting an understanding of codebase, defining project goals, establishing the scope of work, and evaluating the compliance needs.
Analysis – Manual security testing through code logic, finding vulnerabilities and flaws, classifying it based on severity and impacts. Using high reputed open source tools to scan codes for finding low-hanging fruits.
Mitigate – Obliterating flaws and findings, neutralize all loopholes, and offers the best security solutions to clear off the risks associated.
Report – Creating a review report consisting of risk mitigation strategies and strengthening the governance capabilities so as to improve the quality of code.
Support – The unconditional support is provided by the WeSecureApp Team to the Client’s Development Team, till the issue is resolved.
To get your application codes reviewed, hire an expert with WeSecureApp, as we help with full code reviews with security in mind. We have a wide range of expertise to review codes for SQL, Python, C++, Javascript, etc. Learn more.
Build a secure application by Secure Code Review Services : Talk to Our Delivery Head